If you encounter the similar problem, your computer might have been infected by some malware. These malwares break into your computer via different channels like spam emails, peer to peer share files, infected software, or fake update popups.
Once infiltrated, the malware will get into your system or local disk to corrupt and infect your important files. They can also enter your Windows Registry to modify your registry keys and add malicious values. Besides, they will generate multiple conhost.exe, cmd.exe and reg.exe processes in the background. Running on the task manager these processes consume much of your CUP and memory, leaving slow computer and poor PC performance.
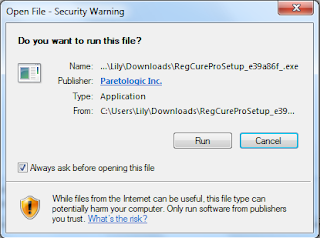
Here are some methods that may help you solve this problem and restore your computer. To remove all the malware (conhost.exe, cmd.exe and reg.exe processes) and speed up your computer, you are recommended to use RegCure Pro to fix your computer.
Method 1: Remove Malware (Conhost.exe, CMD.exe and REG.exe) Step by Step
Method 2: Remove Malware (Conhost.exe, CMD.exe and REG.exe) & Optimize Your PC with RegCure Pro
Method 1: Remove Malware (Conhost.exe, CMD.exe and REG.exe) Step by Step
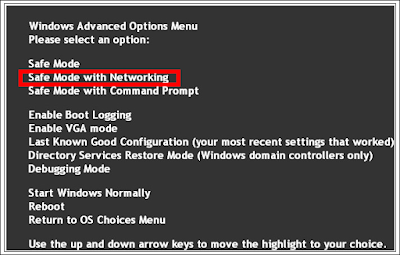
Step 1: Reboot your PC into Safe Mode with Networking
Restart your computer and keep pressing F8. Select Safe Mode with Networking by using the up and down arrow key in your keyboard.
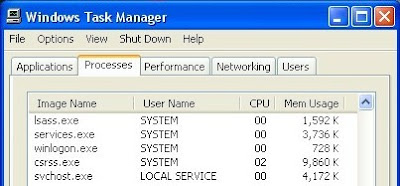
Step 2: Delete suspicious or malicious process related to Malware (Conhost.exe, CMD.exe and REG.exe).
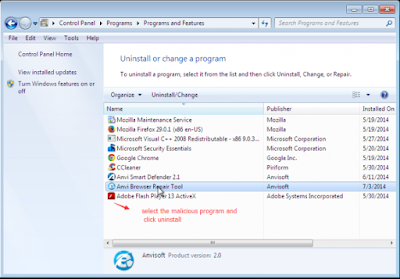
Step 3: Remove suspected programs from control panel.
Press Win & R on your keyboard to open Run. Type in "control" to open control panel and then select Uninstall a program/Program and Features. Search PUP/Malware from the list and remove it.
Step 4: Show hidden folder.
Go to control panel >> Appearance and Personalization >> Folder Options
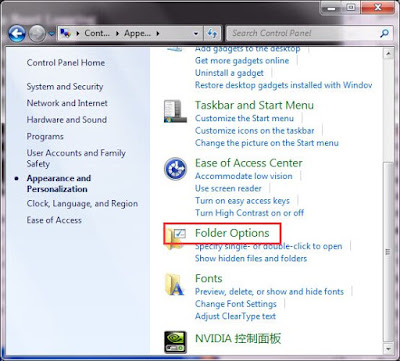
Tick "show hidden files, folders and drives" like the picture below.

Step 5: Delete from local disk.
%AppData%\<random>.exe
%CommonAppData%\<random>.exe
%temp%\<random>.exe
C:\Program Files\<random>
C:\Windows\Temp\<random>.exe
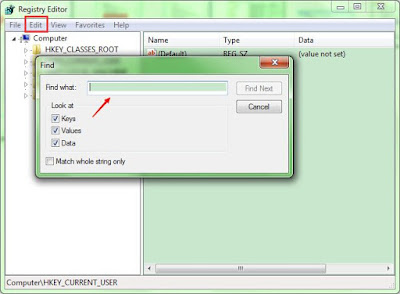
Step 6: Delete infected or additional registry entries.
Press Win & R to open Run, type in "regedit" and hit enter. Click Edit >> Find... to search unwanted keys
Method 2: Remove Malware (Conhost.exe, CMD.exe and REG.exe) & Optimize Your PC with RegCure Pro
RegCure Pro's malware scanner finds active malware and kicks it off your machine. If you also find some registry errors, such as dll file errors in your computer, Regcure Pro will be a good choice to quickly and powerfully clean your windows registry and protect your system files.



(Reference) Watch Video to Fix Malware (Conhost.exe, CMD.exe and REG.exe) Problem
Final Tip:
Malware (Conhost.exe, CMD.exe and REG.exe) Virus can cause a lot of troubles. Usually, the manual tips above may help your get rid of it. But if you fail, you can download powerful remover to get rid of it.


ReplyDeleteAre you willing to know who your spouse really is, if your spouse is cheating just contact cybergoldenhacker he is good at hacking into cell phones,changing school grades and many more this great hacker has also worked for me and i got results of spouse whats-app messages,call logs, text messages, viber,kik, Facebook, emails. deleted text messages and many more this hacker is very fast cheap and affordable he has never disappointed me for once contact him if you have any form of hacking problem am sure he will help you THANK YOU.
contact: cybergoldenhacker at gmail dot com